Source: www.paulosyibelo.com
Introduction: The Bigger Picture
The ever changing cybersecurity landscape requires constant vigilance and knowledge of emerging vulnerabilities. One such recently disclosed threat is DoubleClickjacking, a novel attack technique that uses double-click sequences to bypass traditional clickjacking defences. Discovered by security researcher Paulos Yibelo, this vulnerability poses a significant risk to organisations and individual users alike. It highlights the need for proactive defence.
What is DoubleClickjacking?
DoubleClickjacking is an advanced variation of the classic clickjacking attack that exploits a sequence of two clicks rather than a single click. While traditional clickjacking tricks users into clicking on hidden or obfuscated elements, double clickjacking manipulates the timing between two clicks to bypass known defences such as X-Frame-Options headers and SameSite cookies.
Technical Analysis
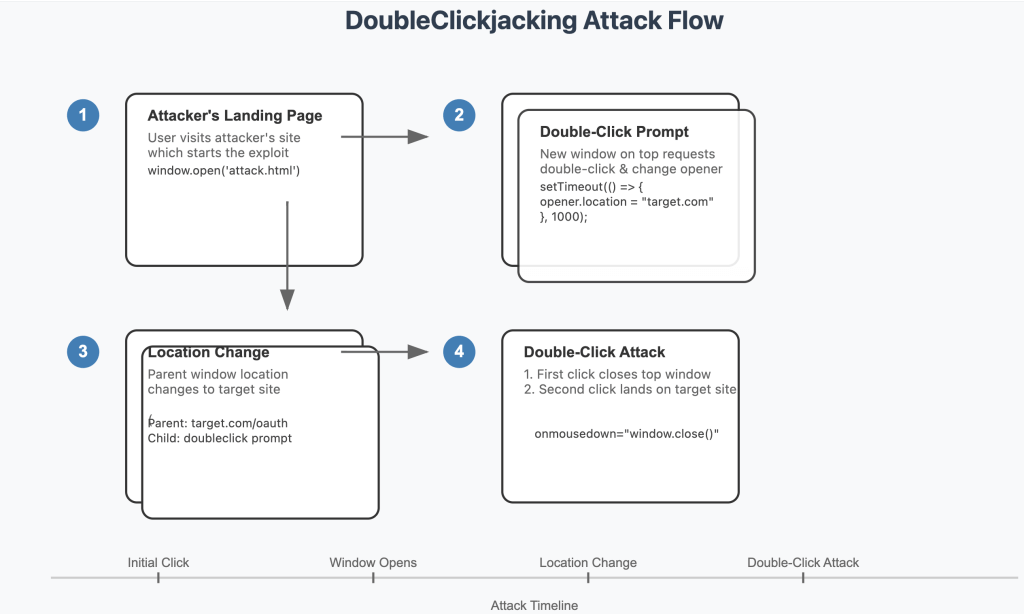
The attack involves:
- A new browser window or tab opening when the user visits a malicious site.
- A deceptive interface that prompts the user to double-click (e.g. a CAPTCHA verification).
- A JavaScript manipulation on the double-click redirects the user to a malicious page. Often, the user authorises a malicious OAuth application or unknowingly approves sensitive actions.
- The top window closes, leaving the user unaware of the unauthorised action.
This seamless swapping of benign UI elements for sensitive ones illustrates the sophistication of DoubleClickjacking.
Exploitation Scenarios
Real-World Examples
Potential scenarios include:
- E-commerce Platforms: Trick users into approving fraudulent transactions.
- Banking Portals: Redirect users to allow unauthorised financial operations.
- Corporate Systems: Gain access to sensitive corporate data through OAuth abuse.
Hypothetical Attack Steps
- Preparation: Attackers create a malicious site that mimics a legitimate interface.
- User Interaction: Victims double-click on an element (e.g., a fake CAPTCHA).
- Exploitation: JavaScript redirects or authorises malicious actions during the double-click sequence.
- Execution: Sensitive operations are completed without the user’s knowledge, such as the authorisation of unauthorised API access.
Example: Slack Account Takeover
Consequences of DoubleClickjacking Exploitation
Impact on Businesses
- Data Breaches: Exfiltration of sensitive customer or corporate data.
- Financial Losses: Unauthorised transactions or fraudulent activity.
- Reputational Damage: Loss of trust due to compromised systems.
Impact on Individual Users
- Privacy Violations: Exposure of personal data.
- Identity Theft: Misuse of credentials for fraudulent purposes.
- Long-Term Risks: Persistent exploitation if vulnerabilities remain unpatched.
Defence Strategies
Website owners can mitigate DoubleClickjacking by taking a proactive, client-side approach:
- Disable Critical Buttons: By default, ensure that critical buttons are inactive unless a mouse gesture or key press is detected. This approach is already implemented by services such as Dropbox.
- Implement User Interaction Validation: Require additional confirmation steps for sensitive actions.
- Regular Updates and Patches: Ensure all software and frameworks are up-to-date to prevent exploitation.
The Role of Cybersecurity Companies
To mitigate the risks posed by vulnerabilities such as DoubleClickjacking, professional cybersecurity services are essential. Key offerings include:
- Penetration Testing:Identification of weak points in systems.
- Security Audits: Comprehensive security posture assessments.
- Vulnerability Assessments: Proactive detection and remediation of threats.
Future Perspectives
DoubleClickjacking is a testament to the ongoing evolution of cyber threats. The industry must remain vigilant and continually develop and deploy new defences. Collaboration with cyber security experts ensures robust protection against new vulnerabilities.
Conclusion
DoubleClickjacking emphasises the importance of proactive cybersecurity measures. Through education and the implementation of layered defences, organisations and individuals can significantly mitigate risk. For tailored security solutions, consult with experts to effectively protect your digital assets.